March 28, 2026 · OPERIUM
KYC-Flow: How to Automate KYC Document Collection for Regulated Businesses — GDPR Compliance, FATF AML Digital Verification, and BSA Audit Trail Requirements in 2026
Know Your Customer compliance is the foundation of every regulated business — and it is also one of the most operationally painful processes in financial services, real estate, legal, and professional services firms. The traditional KYC workflow invo...
Know Your Customer compliance is the foundation of every regulated business — and it is also one of the most operationally painful processes in financial services, real estate, legal, and professional services firms. The traditional KYC workflow involves emailing clients to request documents, receiving blurry phone photos in unencrypted email threads, manually verifying document completeness, chasing missing pages, and storing the collected materials in a file system with no audit trail. This process is not just inefficient — it creates serious legal exposure under GDPR for unencrypted data transmission, under FATF guidelines for inadequate due diligence records, and under BSA requirements for deficient audit trails. KYC-Flow eliminates these risks entirely: create a KYC request defining which documents you need, send a secure token-based link to your client, review and approve uploads with a full SHA-256 audit trail, and export the complete approved KYC package as a ZIP in one click. No client account required. No unencrypted email attachments. No missing audit records. This guide covers the complete technical and legal framework for automated KYC collection, GDPR compliance for sensitive document processing, FATF AML digital verification requirements, and BSA audit trail obligations. Frequently asked questions on token security, SHA-256 integrity, GDPR lawful basis for KYC data, and operational workflow are answered in full.
The Hidden Legal Exposure of Manual KYC Processes
Before understanding how KYC-Flow automates the process, it is essential to understand the specific legal risks that manual KYC workflows create — risks that most regulated businesses are carrying without realizing it.
As detailed in GDPR.eu's guidance on KYC compliance and data protection, the personal data processed during KYC — passport scans, proof of address, company registration documents — constitutes special category data under GDPR Article 9 when it reveals national origin, or sensitive personal data under Article 4 more broadly. The transmission, storage, and access to this data must meet the heightened security standards of GDPR Article 32: encryption in transit, encryption at rest, access controls, and the ability to demonstrate these controls in the event of a Data Protection Authority (DPA) investigation.
Sending a client an email asking them to "attach their passport scan" — the standard manual KYC workflow — fails all four of these requirements simultaneously: standard email is not end-to-end encrypted in transit, email attachments are typically stored in plaintext on email servers, there are no meaningful access controls on who can read the attached document, and there is no audit record of when the document was accessed or by whom.
The FATF guidance on digital KYC verification establishes that regulated entities must implement Customer Due Diligence (CDD) measures that include: identification and verification of the customer's identity using reliable, independent source documents; understanding the nature and purpose of the intended business relationship; and ongoing monitoring to ensure that transactions are consistent with the entity's knowledge of the customer. For digital KYC processes specifically, FATF requires that the digital verification method provides equivalent reliability to in-person document verification — meaning document integrity verification (hash matching), transmission security, and access logging are not optional enhancements but minimum compliance requirements.
The FinCEN guidance on BSA audit trail requirements mandates that financial institutions and other BSA-regulated entities maintain adequate records of their KYC due diligence activities, including: the documents collected, the dates on which they were collected, the identity of the staff member who reviewed them, and the outcome of the review. Manual KYC workflows — email threads, shared drives, paper files — typically lack the timestamping precision and tamper-evidence needed to satisfy BSA audit trail requirements in the event of an examination by FinCEN or a federal banking regulator.
The Five Categories of Legal Exposure in Manual KYC
Exposure 1 — GDPR Article 32 breach: Unencrypted document transmission constitutes a failure to implement appropriate technical measures. Under GDPR, this exposes the data controller to administrative fines of up to 2% of global annual turnover.
Exposure 2 — FATF CDD deficiency: Inability to demonstrate document integrity (no hash verification) creates AML compliance deficiencies. In regulated sectors, this can trigger remedial action requirements, sanctions, or license revocation.
Exposure 3 — BSA audit trail gaps: Missing or incomplete KYC records that cannot demonstrate chain of custody expose the entity to BSA examination findings, civil money penalties, and potential criminal referral in severe cases.
Exposure 4 — Data breach liability: Passport scans and proof of address documents stored in email servers or shared drives are high-value targets for data breaches. Without encryption, access controls, and audit logging, breach liability is substantial.
Exposure 5 — Operational inefficiency penalty: Manual KYC delays client onboarding, increases staff workload, and creates friction that reduces conversion rates for clients who abandon the process mid-way through document submission.
How KYC-Flow Works: The Complete Technical Workflow
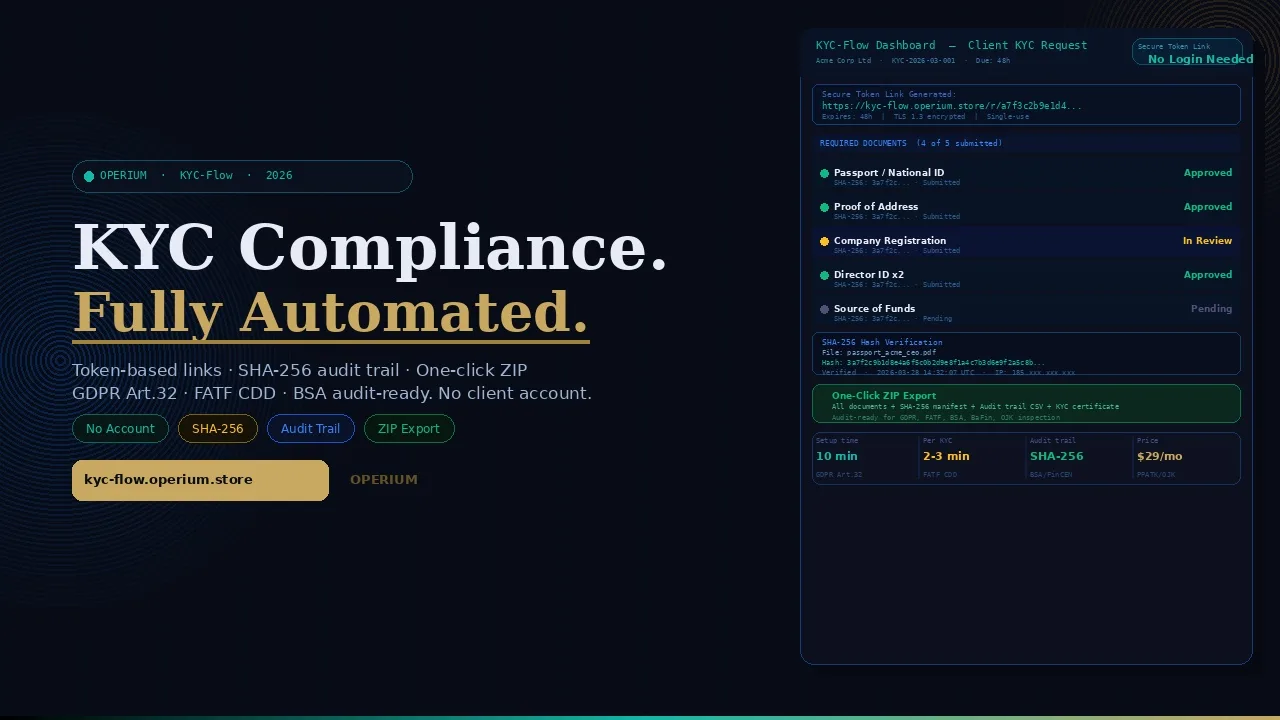
KYC-Flow is a secure, token-based KYC document collection platform that replaces every step of the manual KYC workflow with an automated, audit-logged, GDPR-compliant alternative.
Step 1: Create Your KYC Request
In your KYC-Flow dashboard, define the KYC request for the client. Specify: which documents are required (passport, proof of address, company registration, director identification, bank statement, or any custom document type), the deadline for submission, and any specific instructions for each document type.
KYC-Flow provides standard templates for common regulated business contexts: individual client onboarding (passport + proof of address), corporate entity onboarding (company registration + director IDs + beneficial ownership declaration), and enhanced due diligence (all standard documents plus source of funds documentation).
Step 2: Send the Secure Token-Based Link
KYC-Flow generates a unique, encrypted token for each KYC request. This token is embedded in a secure link sent to the client. The link does not require the client to create an account, register, or remember a password. Clicking the link opens a secure, branded upload portal in the client's browser.
The token is single-use for the upload session and expires after the defined deadline. Each token is cryptographically unique — the same link cannot be reused by a different party, and the token cannot be used to access any other client's data.
Step 3: Client Uploads via Drag-and-Drop
The client sees a clear checklist of required documents with instructions. They upload each document via drag-and-drop or file selection — PDF, JPEG, PNG, and other common formats are accepted. For each uploaded document, KYC-Flow immediately:
- Generates a SHA-256 hash of the file at the moment of upload
- Records the upload timestamp (UTC, millisecond precision)
- Records the IP address of the uploading device
- Stores the file in encrypted storage
The client receives a confirmation screen showing which documents have been submitted and which are still outstanding. No account creation is required at any point.
Step 4: Review and Approve in the KYC-Flow Dashboard
The compliance officer receives a notification when the client completes the upload. In the KYC-Flow dashboard, they review each document against the required criteria: is the document legible? Does the name match the client record? Is the document within its validity period?
For each document, the reviewer either approves or flags it as requiring a re-submission. Every action taken in the dashboard is logged to the audit trail: reviewer identity, timestamp, action taken (approved / rejected / requested re-submission), and any notes.
Step 5: One-Click ZIP Export
Once all documents are approved, KYC-Flow generates a structured ZIP file containing: all approved documents in their original format, the SHA-256 hash log for each document, the complete audit trail (upload timestamps, reviewer actions, IP records), and a KYC completion certificate summarizing the verified identity documents, the verification date, and the reviewing officer.
This ZIP file is the complete, audit-ready KYC record. It can be produced immediately in response to a regulatory examination request, a FATF inspection, or a BSA audit trail requirement.
flowchart TD
A[Create KYC Request in Dashboard] --> B[Define Required Documents and Deadline]
B --> C[KYC-Flow Generates Encrypted Token Link]
C --> D[Send Secure Link to Client - No Account Needed]
D --> E[Client Uploads via Drag and Drop]
E --> F[SHA-256 Hash Generated at Upload]
F --> G[Timestamp and IP Logged to Audit Trail]
G --> H[Compliance Officer Reviews in Dashboard]
H --> I{Document Approved?}
I -->|Yes| J[Document Approved - Action Logged]
I -->|No| K[Re-submission Requested - Action Logged]
K --> E
J --> L[One-Click ZIP Export with Full Audit Record]
L --> M[Audit-Ready KYC Package]
style A fill:#c9a962,color:#0c0e14
style L fill:#10b981,color:#fff
style M fill:#10b981,color:#fff
GDPR Compliance for KYC Data Processing: The Complete Framework
KYC data collection involves some of the most sensitive personal data categories under GDPR. Understanding the legal framework is essential for every regulated business collecting KYC documents.
Lawful Basis for KYC Data Processing
For regulated businesses, KYC data collection has a clear lawful basis under GDPR Article 6(1)(c): processing is necessary for compliance with a legal obligation to which the controller is subject. AML regulations (4th and 5th EU AML Directives, national transpositions) impose a mandatory legal obligation to collect and verify customer identity documents. This legal obligation basis is the most robust available under GDPR — it cannot be overridden by the data subject's objection right, and it does not require consent.
However, the legal obligation basis does not eliminate all other GDPR requirements. The controller must still comply with: the data minimization principle (collect only documents specifically required by the applicable regulation), the storage limitation principle (retain documents only for the period required by law — typically 5 years after the end of the business relationship under EU AML Directives), and the security principle (implement appropriate technical and organizational measures to protect the documents).
GDPR Article 32 Security Requirements for KYC
GDPR.eu's KYC compliance guidance identifies the specific Article 32 security measures required for KYC document processing:
- Encryption in transit: All document uploads must use TLS 1.2 or higher. KYC-Flow enforces TLS 1.3 for all client upload sessions.
- Encryption at rest: Stored documents must be encrypted at the storage layer. KYC-Flow uses AES-256 encryption for all stored documents.
- Access controls: Only authorized personnel should be able to access KYC documents. KYC-Flow implements role-based access with a complete access log.
- Audit logging: Every access, every review action, every export must be logged. KYC-Flow's audit trail is immutable and timestamped.
- Integrity verification: Document integrity must be verifiable — SHA-256 hashing provides cryptographic proof that a document has not been altered since upload.
- Data subject rights: Clients must be able to exercise their right of access and right to erasure. KYC-Flow's dashboard allows authorized staff to retrieve or delete individual client records.
Retention and Deletion
Most EU AML Directives require KYC records to be retained for 5 years after the end of the business relationship. KYC-Flow's retention settings allow you to define automatic deletion triggers aligned with your legal retention obligation. Automated deletion is logged to the audit trail — demonstrating compliance with the storage limitation principle.
Comparative Analysis: KYC-Flow vs Alternative KYC Approaches
| Criterion | KYC-Flow | Email + Shared Drive | DocuSign / eSign | Full KYC SaaS (Jumio, Onfido) |
|---|---|---|---|---|
| Client account required | No | No | Yes | Yes |
| Token-based secure link | Yes | No | Partial | Yes |
| SHA-256 file integrity | Yes | No | No | Partial |
| Full audit trail | Yes | No | Partial | Yes |
| GDPR Article 32 compliant | Yes | No | Partial | Yes |
| FATF CDD ready | Yes | No | No | Yes |
| One-click ZIP export | Yes | Manual | No | No |
| Setup complexity | Low | None | Medium | High |
| Price | $29/mo unlimited | $0 (risk cost) | $30-50/mo | $500-5,000+/mo |
| Integration required | No | No | No | Yes |
Integrating KYC-Flow with the OPERIUM Compliance Stack
Contract-Sign: KYC verification and contract execution are sequential steps in client onboarding for regulated businesses. KYC-Flow handles the identity verification phase; Contract-Sign handles the agreement execution phase — delivering the engagement letter or terms and conditions for electronic signature with its own SHA-256 audit certificate.
Proof-of-Service: For professional services firms where KYC is a prerequisite for service delivery, Proof-of-Service documents that the verified client received and acknowledged the service deliverable — creating a legally defensible chain from KYC verification through to service acknowledgement.
MonthlyDocs: For accountants and bookkeepers who must perform KYC on new clients, KYC-Flow handles the initial identity verification and MonthlyDocs handles the ongoing monthly document collection — the two tools together covering the full client lifecycle from onboarding to ongoing compliance.
Partner-Portal: Agencies and advisory firms that conduct KYC on behalf of clients can use KYC-Flow for document collection and Partner-Portal for delivering the KYC completion report and ongoing compliance deliverables to the end client in a branded, professional environment.
InvoiceBot: For regulated businesses where billing is contingent on completed KYC, the KYC-Flow completion notification can trigger the billing workflow — invoicing for the KYC service itself or releasing the invoice for the main engagement once identity verification is complete.
FAQ — Frequently Asked Questions
What is token-based KYC document collection and why is it more secure than email?
Token-based collection means each client receives a unique, cryptographically generated link that grants access only to their specific KYC upload portal. Unlike email attachments — which are transmitted unencrypted between mail servers and stored in plaintext in email archives — KYC-Flow's token links use TLS 1.3 encryption for all data in transit, AES-256 encryption for data at rest, and expire after the defined deadline. The token cannot be reused or repurposed by any other party.
Is KYC-Flow compliant with GDPR for processing passport scans and proof of address?
Yes. KYC-Flow's data processing architecture is designed to meet GDPR Article 32 requirements: TLS 1.3 in transit, AES-256 at rest, role-based access controls, immutable audit logging, and SHA-256 document integrity verification. The lawful basis for KYC data collection under GDPR is Article 6(1)(c) — legal obligation — which applies to all regulated businesses subject to AML/KYC requirements. As confirmed by GDPR.eu's KYC guidance, this is the most appropriate and robust lawful basis for mandatory KYC document collection.
What does SHA-256 hashing provide in the context of KYC compliance?
SHA-256 is a cryptographic hash function that generates a unique 64-character fingerprint for any file. For KYC compliance, it provides: tamper evidence — if a document is modified after upload, its SHA-256 hash will not match the hash recorded at upload, proving tampering occurred; chain of custody — the hash recorded at upload, combined with the upload timestamp and IP, creates a cryptographically verifiable record of the document's integrity from the moment of submission; and audit readiness — regulators and courts accept SHA-256 hashes as proof of document integrity.
How does KYC-Flow satisfy FATF requirements for digital Customer Due Diligence?
As established by FATF's digital KYC guidance, digital CDD must provide equivalent reliability to in-person verification. KYC-Flow satisfies the key FATF digital CDD requirements: document integrity verification via SHA-256 hashing, secure transmission via TLS 1.3, identity of the submitting party via IP logging and token authentication, reviewer identity and action logging, and a complete exportable audit record.
Does the client need to create an account to submit KYC documents?
No. This is a core design feature of KYC-Flow. The secure token link provides session-authenticated access to the client's specific upload portal without requiring any account creation, password, or registration. This reduces friction in the KYC submission process — a significant factor in client completion rates — while maintaining security through token cryptography.
How long does it take to set up KYC-Flow for a new client onboarding workflow?
The initial account setup takes approximately 10 minutes. Creating a new KYC request for a specific client takes 2–3 minutes (selecting required documents from templates and entering the client's contact details). The client receives the secure link within seconds of the request being created.
What file formats does KYC-Flow accept for document uploads?
KYC-Flow accepts PDF, JPEG, PNG, TIFF, and HEIC formats for document uploads. There is no file size limit per document for Pro plan users. The platform automatically validates that uploaded files are readable (non-corrupt) at the point of upload.
How does the one-click ZIP export work and what does it contain?
When all required documents for a KYC request have been approved, the compliance officer can generate the KYC package with a single click. The ZIP file contains: all approved documents in their original formats; a SHA-256 hash manifest listing every document's hash, upload timestamp, and uploader IP; the complete audit trail in CSV format showing every action taken by every reviewer; and a KYC completion certificate in PDF format summarizing the client identity, documents verified, verification dates, and reviewing officer identity.
Is KYC-Flow suitable for corporate KYC with multiple beneficial owners?
Yes. KYC-Flow supports complex corporate KYC structures with multiple document requestees. A single KYC request can include document requirements for the entity itself (company registration, articles of association) and for each beneficial owner (individual passport and proof of address), each with their own secure upload link. All documents flow into a single consolidated KYC record with a unified audit trail.
What happens if a client uploads an incorrect or illegible document?
The reviewing compliance officer can reject the document with a specific note explaining the issue (e.g., "passport image too blurry — please re-photograph in good lighting"). The client receives a notification and can re-upload the corrected document using the same secure token link (if it has not expired). Every rejection and re-submission is logged to the audit trail with timestamps and reviewer notes.
Conclusion: From Legal Exposure to Audit-Ready Compliance
The gap between manual KYC workflows and regulatory requirements is not a minor procedural gap — it is a structural legal exposure that affects virtually every regulated business currently collecting identity documents via email. GDPR Article 32, FATF CDD requirements, and BSA audit trail obligations collectively demand encryption, integrity verification, access controls, and immutable audit logging. Manual workflows provide none of these.
KYC-Flow closes this gap at $29/month for unlimited KYC requests. The cost of a single DPA investigation finding, a FATF remediation requirement, or a BSA civil money penalty dwarfs any annual subscription cost. More importantly, KYC-Flow reduces client friction, accelerates onboarding timelines, and produces professional, regulation-ready KYC packages that demonstrate your firm's commitment to compliance to every regulator, auditor, and counterparty who reviews them.
Explore the complete OPERIUM compliance and operations ecosystem for 20 SaaS tools covering every phase of client onboarding, service delivery, and ongoing compliance.